Who's Spying on Your Messages? Comparing Privacy Between Chat Apps
Want to know how to stop the NSA from spying on your messages? What are you waiting for? Click me already!

I've always had a love/hate relationship with Facebook Messenger. There was always a feeling of unease knowing that Zuck could look at my private messages. Yet, it seemed that everyone was using Messenger. It was like being stuck between a rock and a hard place. Either surrender your privacy or be isolated from your friends.
Recently I choose to bite the bullet and move off of Facebook Messenger. It wasn't the easiest thing to do, but it gave me the power to communicate with greater peace of mind. Messaging apps are a staple of every day life. Regardless of your personal choices, I believe it's important to be an informed user. Below, we compare many popular messaging options and their implications on your privacy. You can come to your own conclusions afterwards.
Some Fundamental Concepts
Let's define some terms so we're on the same page. They're necessary to understand how different messaging apps work. If you're an engineer, forgive the lack of rigor. I'm explaining these in plain English, so everybody can understand.
Encryption
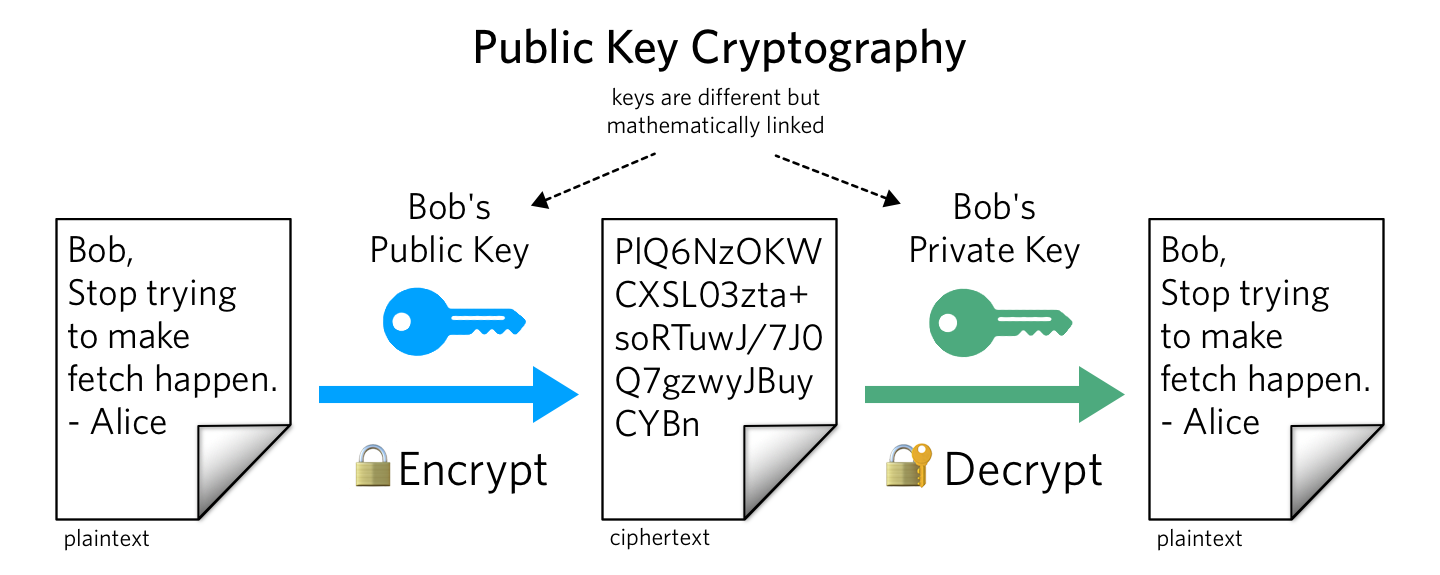
When you encrypt a message, only the intended recipient can read the message. The original plaintext message turns into an opaque blob of data. The recipient with the proper credentials can decrypt the blob back into the original message.
In practice, most data that travels over the Internet is encrypted. The Transport Layer Security (TLS) protocol encrypts most data you send to websites. As a result, random people on your network cannot see what you write.
End-to-end Encryption
For most types of messaging, you send a message to a server. The server routes the messages to your recipient. Although TLS can prevent random parties from reading your message, the server can have full control over your message.
End-to-end encryption (E2EE) handles that problem. You and your recipient exchange encryption keys beforehand. When any message reaches a server, the server only sees the encrypted blob. Therefore, nobody needs to trust a third party service.
Open Source
Software that's open sourced means that the public can view the source code for the software. This is especially relevant for software running on remote servers. The public can audit whether the server has any security issues and whether it works as intended. For software that isn't open source, you need to trust that it does what it claims to do.
Chat App Privacy Compared
The average consumer has a boatload of choices when messaging others. Not all messaging apps are built the same, but fortunately some are quite similar. We'll examine the following messaging options:
- SMS
- Social apps (e.g. Facebook, WeChat, Snapchat)
- "Enhanced SMS" (e.g. iMessage and RCS)
- Telegram
- Signal
- Keybase
If you're too lazy to read the details, here's a chart with the general verdict. Skip to the end if you want my overall recommendations.
| Encrypted | End-to-end encrypted | Open source | Secure metadata | |
|---|---|---|---|---|
| SMS | ❌ | ❌ | ❌ | ❌ |
| Facebook/etc... | ✅ | ❌ | ❌ | ❌ |
| iMessage/RCS | ✅ | ⚠️ | ❌ | ❌ |
| Telegram | ✅ | ⚠️ | ⚠️ | ❌ |
| ✅ | ✅ | ❌ | ❌ | |
| Signal | ✅ | ✅ | ✅ | ✅ |
| Keybase | ✅ | ✅ | ⚠️ | ⚠️ |
Here is the key to the above chart:
- ✅: Supported
- ❌: Not supported
- ⚠️: Supported, but with caveats
SMS
SMS is the original text messaging protocol. Before smartphones, we could send still send texts, albeit in a more primitive manner. If you have a phone, you can probably use SMS, which makes is a very common option. But that's where the benefits end. SMS is a security disaster. Text messages aren't encrypted. Anybody who intercepts your message knows what you're sending. The same idea applies to the cell carriers. Your texts remain on their servers. I'd recommend using alternatives to SMS whenever possible.
Pros
- Convenient
- Almost everybody can use SMS
Cons
- Primitive compared to other alternatives
- No encryption whatsoever
- Cell carriers store your text messages
Social Apps

As social media and smartphones gained traction, many apps began to support messaging. These apps may have different features, but they're identical from a security perspective. Thus, we put them all in the same bucket. Some of these apps include:
- Facebook Messenger
- Snapchat
- Line
- Slack
- Discord
It's a step up from SMS, but not by much. Instead of your messages traveling through cell towers, it goes through TCP/IP. As a result, you have the benefit of encryption through TLS. Random people will not be able to read your messages. However, your texts will still be stored in some tech company's server. You exchange one master for another master.
The problem with these apps it that they require you to trust the company offering the service. You must believe that a rogue employee won't read your messages. You need to trust that their code works correctly. If Facebook gets hacked or receives a warrant, don't expect them to be too respectful of your privacy.
Pros
- Popular
- Good user experience
- Data is encrypted
Cons
- The server sees all your data
- Code is not open source
- You need to trust the service
iMessage and RCS
Modern phone manufacturers have been aware of the security limitations of SMS. As a result, they've built their own enhancements on top of the traditional text message.
Apple build iMessage for iPhone users. Users of iMessage get to sync their texts across all Apple devices. All messages are end-to-end encrypted, so Apple can't see what you send. However, the encryption only happens when both users are on iPhones. Additionally, enabling iCloud backup on your iMessages gives Apple your encryption key. Thus enabling backups disables end-to-end encryption.

Google is developing support for the RCS protocol on Google-manufactured phones. Samsung is doing something similar for the default text message app on their phones. Phones using RCS will eventually have end-to-end encryption, but there's currently limited support. The privacy benefits of RCS seem promising, but its current state leaves more to be desired.
Pros
- Better user experience than SMS
- Can fall back to SMS if necessary
- End-to-end encrypted (if both users use the same app)
Cons
- Code is not open source
- RCS is still in development
- Ecosystem lock (you need an iPhone for iMessage or select apps for RCS)
Telegram

Telegram has become a popular messaging app for groups. It supports end-to-end encryption as an option, so Telegram cannot read your messages. On the other hand, it's not the default. You have to manually enable end-to-end encryption. The Telegram client is open source, allowing people to audit the code. However, its server is not open source. Users still need to trust Telegram to a degree. Telegram is above average, but we can still do better.
Pros
- Supports end-to-end encryption
- Client is open source
Cons
- End-to-end encryption isn't the default
- Server is not open source
- Encryption scheme has had a history of security concerns

WhatsApp is quite popular and has become the default "international" chat app of sorts. From a privacy perspective, it's pretty good. All messages are always end-to-end encrypted, unlike Telegram. It used to be the ideal messaging app.
Unfortunately, in 2014, Facebook acquired WhatsApp. The app's terms of service changed, and now Facebook will have access to your metadata. For example, they will know who you talk to and when you talk to them. I can see this data being used to profile users. Eventually it may be enough for advertisement targeting. WhatsApp also claims not to store your messages on their servers. Unfortunately, since their code is not open source, there's no way to prove that claim.
Pros
- Popular, especially internationally
- All messages are end-to-end encrypted
Cons
- Not open source
- Facebook has access to your metadata; questionable incentives
- You need a valid phone number
Signal

After the acquisition of WhatsApp, one of the cofounders started the Signal Foundation. Signal was made with privacy in mind, and it has the best benefits among all other messaging apps. In addition to end-to-end encryption, Signal encrypts all metadata as well. As a result, the server cannot determine anything about the people using the service.
All of Signal's code (including the server) is open source, so everything can be audited. There are also nice security features like exploding messages. If your phone gets compromised in the future, attackers will not be able to find your messages. I'm a fan of Signal. Its privacy guarantees are the cream of the crop.
Pros
- Everything is end-to-end encrypted, including all metadata
- Everything is open source (including server code)
- Can fall back to SMS
Cons
- Not as popular as the other apps
- You need a valid phone number
Keybase
Keybase is a jack-of-all-trades cryptography app that supports end-to-end encrypted messaging. Like with Signal, it also supports exploding messages. Keybase also supports features unrelated to messaging like file encryption and identity verification.
The main concern with Keybase has a similar story with WhatsApp. In 2020, Zoom acquired Keybase. Thus the incentives and future of Keybase remain unclear. The Keybase servers are also not open source, meaning the public cannot audit the code. It also means that if Zoom does shut down Keybase, nobody will be able to host a Keybase replacement.
Pros
- End-to-end encrypted
- Client is open source
- Other benefits like encrypted storage and crypto wallets
Cons
- Owned by Zoom; questionable incentives
- Not popular (pretty much limited to security nerds)
- Server is not open source
Making a Switch
Great, so you've read about more messaging apps than you'd care to see. Now what?
If you're happy with what you're using or don't care, keep doing what you're doing. There's no need to change anything. Privacy is a personal decision, so I'm not going to indoctrinate you.
If you do have some interest in making a change, you'll want a plan. Disappearing off the face of the earth isn't doing anyone a favor. While you make the switch, keep these three principles in mind.
- Migrate incrementally.
- Prefer certain apps, but continue to support them all.
- Stay practical.
Migrate Incrementally
You may be tempted to immediately switch away from all your current messaging apps. In practice, it'll only confuse the people you message and cause chaos.
Instead, look to gradually migrate away from your old chat apps. For example, first tell your closest friends that you're moving off the old app. Then have future conversations with them on the new app. Direct messages are easier to migrate, so start with those before group chats.
Prefer Some, Support All
It may not be feasible to cut off a messaging channel completely. Some people may refuse to use a different app, or they may be too lazy to switch. I don't recommend abandoning communication because of that. Continue to support your old messaging apps. You don't have to be as responsive, and it should be okay as long as you don't have any expectation of privacy.
In general, here's my preference of messaging apps. It's based off my historical usage and privacy benefits.
- Signal
- Everything else
If a friend uses Signal or WhatsApp, that's ideal. If not, I encourage them to download Signal, but I won't otherwise change my behavior if they refuse to switch.
Stay Practical
Above all, stay practical. There's always a trade-off when you try to get more privacy. Sometimes it's better to use a tool without an expectation of privacy. For example, it's probably a bad idea to refuse to use Slack for work. Your gaming experience may get worse without Discord. It would be weird not to talk to someone you just met on Twitter.
At the end of the day, what matters is that you use the right tool for the job while being an informed user. Happy texting!
If you enjoyed this blog post, follow me on Twitter and send me an unencrypted DM. 🐦

Comments ()